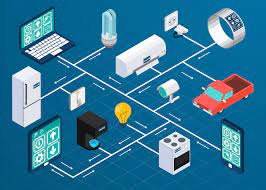
Smart Devieces in your WiFi Network
/!\ This is for educational purposes only, and should not be used for unauthorized access, tampering or accessed illegally without owner permission.
Smart devices make our lives easier but there is a dark side. They are often poorly-secured and offer a backdoor to your network that wouldn’t otherwise exist.
You might have an incredible firewall, great antivirus software, and even a VPN, but your network is probably not as secure as you think it is.
There are 21.5 billion Internet of Things (IoT) devices installed worldwide.
Many of them are consumer products, including security and entertainment devices.
They can make our lives easier, but many of them have atrocious security. What’s worse, each unprotected device represents an entry point that attackers can exploit.
Why Are IoT Devices a Security Risk?
You might be asking yourself how a hacker can exploit your smart fridge or speaker. The answer comes down to hard-coded credentials and in-built flaws. Take the example of the Opticam i5. A report by F-Secure found 18 flaws in this device and the Foscam C2.
The biggest vulnerability was the use of non-random default hardcoded passwords. These passwords allowed admin access to the web user interface and its user account for the built-in FTP camera server.
The default passwords were blank, meaning an attacker would only need to type the word “admin” to gain access to the camera’s features. This danger exists regardless of how strong other users’ passwords are.
This problem is not just limited to cameras. Many IoT devices, especially cheap devices manufactured in China, have poor security features. It is almost impossible for the average user -- or even professional security teams -- to ensure that IoT devices are up-to-date. And that’s if the manufacturer is even offering security patches -- and many don’t.
Even Security Professionals Struggle With IoT Devices
Insecure IoT devices are a huge problem. They are constantly connected to the internet and over half of these devices have vulnerabilities, making them an easy target for attackers.
This situation has led to an epidemic of infected devices. IoT devices now make up around 33% of all infected devices globally. To make matters worse, 98% of all IoT devices have unencrypted traffic which can reveal sensitive data if they are breached.
Lack of adequate security is partially why 99% of security professionals are encountering challenges when dealing with IoT devices. Even with their own networks, 55% of security professionals can’t monitor connected systems entering their controlled environment.
This problem is compounded by a proliferation of cheap, poorly-secured, devices originating from China.
The more connected the device is, the more it can cause security problems. For example, if a hacker compromises a Ring camera, they can then use the microphone to control your smart speakers, allowing them to control any smart device in your home.
To see this technique in action you need to look no further than the Burger King ad that activated your Google home speaker to tell you about the Whopper.
How Can I Secure My IoT Devices?
IoT devices do represent a challenge to home WiFi networks, but there are some steps you can take. It starts even before you buy your device: do good research. It can be tempting to buy a cheap device from Wish.com or AliExpress, but these are the most likely to have security problems.
However, even devices from big manufacturers, like Amazon, can have security flaws. All of which means that you should take a proactive approach in securing your network:
Step 1 - Change Your Router Details
It may seem odd, but your router's name alone could be enough to give an attacker access. That’s because the default settings often name your wifi connection after the manufacturer of the router or the network that you’re using.
Leaving the default network name in place can give an attacker clues that will make it easier to compromise your network. You should change the network name to something memorable that doesn’t give away any personal information.
Step 2 - Secure Your Devices
The first thing you should do when bringing a new device into your home is to secure it. Log in and immediately change the default admin and user passwords to more secure ones. You can do that with our free password generator tool.
This one step will protect you from the most common attacks which rely on people not changing the default settings.
You should also check for security updates as soon as possible.
Lastly, remember that each device needs a unique password.
Step 3 - Don’t Use Public WiFi Without a VPN
Using open public WiFi is a lot riskier than you might think. These networks are relatively easy to break into and they give attackers a full view of all the traffic on the network.
If you log into your IoT network over public wifi, an attacker can potentially acquire your login credentials. The best way to avoid this danger is to use a Virtual Private Network (VPN) which will encrypt all your internet traffic and prevent eavesdroppers from intercepting your communications.
Step 4 - Keep Your IoT Devices On a Guest Network
Guest networks are useful tools to protect your networks when people come to visit -- and you should be using them already.
What you may not have realized is that you can also use guest networks to isolate your IoT devices. That way, even if a smart device is compromised, the attacker will be stuck in the guest network and unable to access any of your primary network traffic or account credentials.
Step 5 - Use Two-Factor Authentication
The final step is two-factor authentication (2FA). You should secure your top-level network protection via text message or a biometric login. Your network will not only alert you to any malicious login attempts, but it can make it far more complicated for an attacker to gain control of your IoT network.
If you follow these steps, you are well on the way to securing your home WiFi network, no matter how many IoT devices you decide to fill it with.